End of Life for Akamai Identity Cloud
https://techdocs.akamai.com/identity-cloud/docs/product-status
End of Life for Akamai Identity Cloud
https://techdocs.akamai.com/identity-cloud/docs/product-status
Default passwords (in this case voicemail PIN) strike again! There are many #AuthN systems around that support sending OTPs by a phone call as an alternative/fallback to SMS (and is an accessibility requirement). Unfortunately, they can't account for this attack vector.
(Oh, and use Signal, not Telegram)
#Identity #Security
https://gbhackers.com/hackers-hijack-telegram-accounts/

Via Austin Kocher:
#USCIS just sent out an email announcing that it only recognizes "two sexes - male & female" & generally only sex assigned at birth.
The insatiable hunger to feed #LLMs and #AI is parasitically draining the commons and public internet. Bandwidth costs are spiking as crawlers take data for training and information. For Wikipedia, the lack of attribution means no visitors, no donors, just cost. The #ethics of AI are failing here.
I saw Tim Karr on bluesky suggest that AIs should pay fees or a tax (should that be tariffs?) into a fund that supports public content. Services like Cloudflare and Fastly that defend against bots are evolving for crawlers. In #identity, the implications for #AgenticAI, #AI, and #NHI are vast.
https://diff.wikimedia.org/2025/04/01/how-crawlers-impact-the-operations-of-the-wikimedia-projects/

Transgender activist and TED Resident Samy Nour Younes shares the remarkable, centuries-old history of the trans community.
https://www.ted.com/talks/samy_nour_younes_a_short_history_of_trans_people_s_long_fight_for_equality #TED #Transgenderl #LGBTQ #History #TransHistory #Identity #Equality
“So on this #TransDayOfVisibility, I see you — the person behind the governmental erasure and deafening public silence. I see your complexity, your resilience, your #humanity that extends far beyond your #gender #identity. And I promise to keep fighting for a world where being seen doesn't come with a side of existential dread.
Because one day, visibility won't be an act of #courage. It will just be #life.”
https://www.readtpa.com/p/navigating-trans-day-of-visibility
"The boys laughed and, as the teacher removed one of them from the class, other students laughed. It wasn’t the note that stayed with my daughter. It was the laughter."
Aaron Rabinowitz writes about #tattoos, #signs, #identity, and #survival: https://longreads.com/2025/03/27/tattoos-signs-history-antisemitism/?utm_source=mastodon&utm_medium=social
Nouveau
Great Australian Pods Podcast Directory: https://www.greataustralianpods.com/nouveau/
What identity do we truly want? That of an isolated country or that of a stronger, more united European community?
#eu #europeanunion #europe #politics #economy #society #identity #humanrights #peace #defenddemocracy
https://officinaprogetti.org/en/divided-and-vulnerable-europes-radical-right-and-sovereignists/

Educating myself on becoming a person with a disability.
#amyloidosis
#disability
#identity
#inclusion
#invisibility
open.substack.com/pub/recently...
Educating myself on becoming a...
The Design of the New Swiss Passport
https://kottke.org/25/03/the-design-of-the-new-swiss-passport
In this new Longreads essay, Aaron Rabinowitz writes about survival, identity, and the inked and invisible scars that history leaves behind.
Krzysztof Grzybacz’s large-scale oil paintings invoke tenderness and curiosity.
https://www.thisiscolossal.com/2025/03/krzysztof-grzybacz-floral-compositions/
"Dry-erase ink is not similar to tattoo ink, but it is almost identical to ink from a permanent marker. And if you leave it on a surface for long enough, especially a porous surface, it will remain. The brain is a porous surface. Memory is a porous surface."
A new essay by Aaron Rabinowitz: https://longreads.com/2025/03/27/tattoos-signs-history-antisemitism/?utm_source=bluesky&utm_medium=social
https://www.europesays.com/1944016/ Goldman Sachs’ Marco Argenti Said Companies Must Embed Culture Into AI #AI #AIAgent #ArtificialIntelligence #BusinessInsider #CompanyCulture #Cybersecurity #GoldmanSachs #HumanWorker #identity #LastYear #LeadershipPrinciple #lens #MarcoArgenti #Organization #TechIndustry #Workforce #workplace
@BjornW :
I've stopped doing that after a lot of people called me an idiot and a liar if I kindly notified them. I stopped, I'll get scolded anyway.
Big tech and most admins want everyone to believe that "Let's Encrypt" is the only goal. Nearly 100% of tech people believe that.
And admins WANT to believe that, because reliable authentication of website owners is a PITA. They just love ACME and tell their website visitors to GFY.
People like you tooting nonsense get a lot of boosts. It's called fake news or big tech propaganda. If you know better, why don't you WRITE BETTER?
It has ruined the internet. Not for phun but purely for profit. And it is what ruins people's lives and lets employees open the vdoor for ransomware and data-theft.
See also https://infosec.exchange/@ErikvanStraten/112914047006977222 (and, in Dutch, https://security.nl/posting/881296).
Whether at work, with friends or when shopping online - your e-mail is more than just a communications tool. It is your digital ID, the key to online services and often the first impression you make. A personal e-mail address creates trust and underlines your identity.
Find out in our blog how you can strengthen your digital presence with your own domain: https://mailbox.org/en/post/email-address-with-your-custom-domain-introduction-and-tips
#mailboxorg #OwnDomain #E-mailBrand #Identity #TipsAndTricks
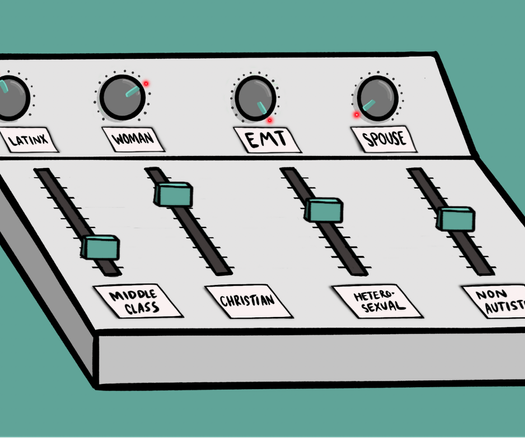
Really good article that I just read which dives into autistic versus non-autistic identity, it puts out a theory that Autistic identity is value-and-passion-driven versus non-Autistic identity being focused on collective identity membership, and the way the two conflict and differ.
(20 Mar) Robert Peterson Summons Black Resilience and Tenderness in Vibrant Portraits
Peterson’s striking oil paintings invite us into emotionally complex inner worlds.
https://s.faithcollapsing.com/52hys
Archive: ais: https://archive.md/wip/9CzgD ia: https://s.faithcollapsing.com/zndp5
#art #identity #painting #portraits #robert-peterson
An international cohort of writers learn with and care for each other in Tokyo and beyond. https://www.japantimes.co.jp/community/2025/03/24/voices/mixed-race-identity-storytelling-workshop/?utm_medium=Social&utm_source=mastodon #community #voices #hafu #identity #mixedrace #writing #travelwriting #teaching
